Inside Flowtriq: Distributed Host-Agent DDoS Detection and Automated Mitigation
Flowtriq — Security
CHAPTERYour edge router isn’t a silver bullet. A 2‑minute host agent might be.
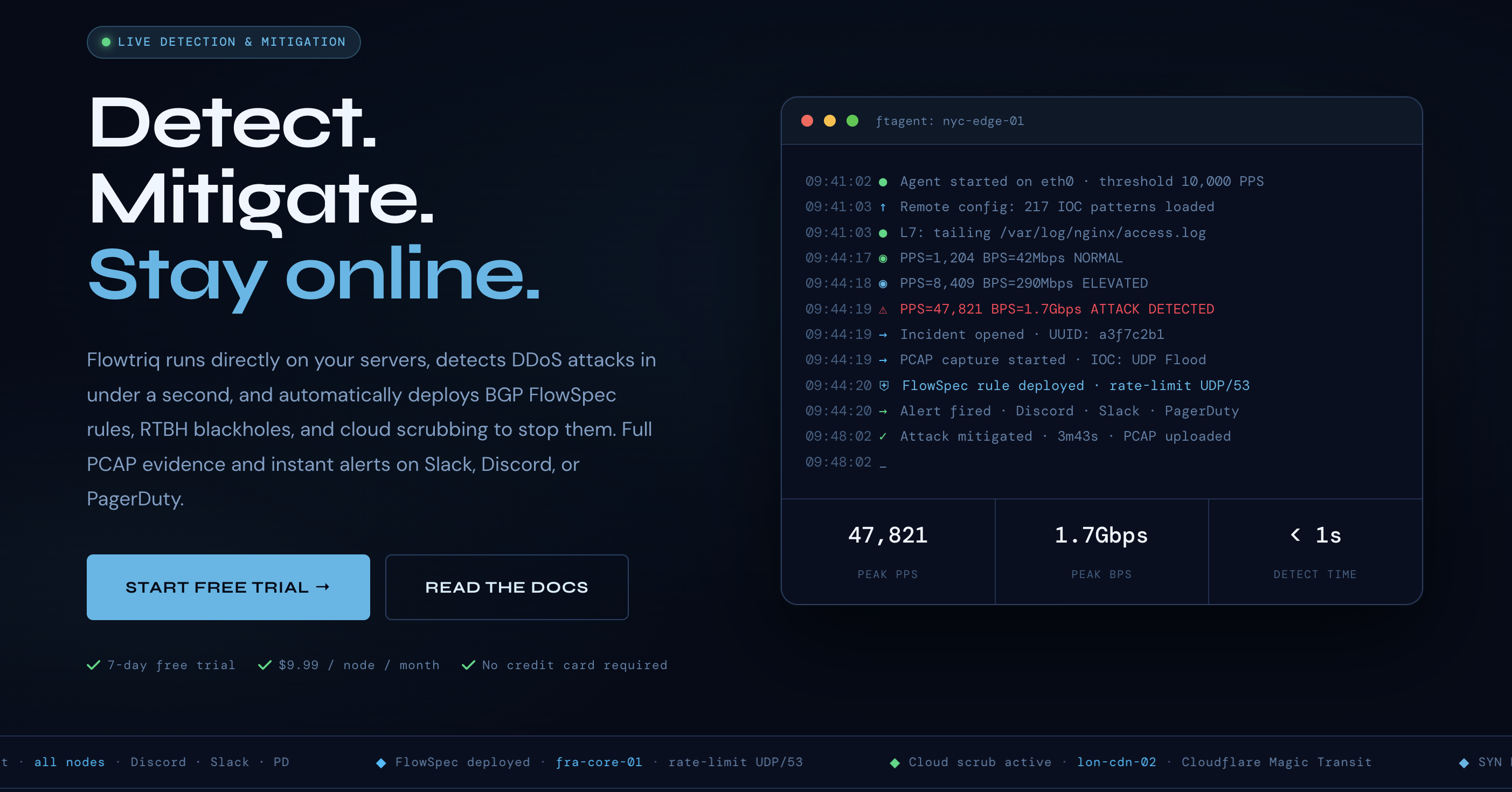
Most DDoS defenses worship the perimeter—big iron scrubbing, anycast, and carrier filters. The data shows the faster path is often nearer the workload. Flowtriq takes the contrarian route: a lightweight Python agent (ftagent) on each Linux server, reading packets directly off the NIC and making sub‑second decisions before users feel pain. Core design principles are agent-first signal capture, baseline-driven anomaly detection, and automated network-layer enforcement via BGP FlowSpec, RTBH, and scrubbing service handoffs. In practice, it’s a Platform Tool for infrastructure teams that need deterministic, per-node protection without manual threshold tuning. Architecture choices emphasize minimal deployment friction (install in under two minutes), packet-level visibility, and an “automation-first” posture—runbooks, immutable audit logs, and status pages—aligned with Marketplace Tech realities and evolving Platform Trends.
CHAPTERArchitecture & Design Principles
Flowtriq’s architecture operates on two planes:
- Data plane: ftagent runs on any Linux host, inspects packets from the NIC (raw socket/pcap-level), and computes per-second PPS/bitrate feature vectors. It learns dynamic baselines per host and flags deviations across 8+ attack classes (SYN/UDP/ICMP floods, DNS/memcached amplification, HTTP floods, multi-vector, Layer 7 variants). IOC correlation runs locally against a 642k+ indicator set to speed early classification.
- Control plane: A cloud dashboard orchestrates policies, escalation steps, and multi-node coordination. On detection, it can push BGP FlowSpec, trigger RTBH, or pivot to provider scrubbing (Cloudflare Magic Transit, OVH VAC, Hetzner) per escalation policy. Full PCAP capture is auto-triggered for forensics, and all actions are recorded in an immutable audit log.
Scalability follows a distributed, host-centric pattern: detection remains local (no single choke point), while orchestration is centralized. This keeps decisions close to the workload and enables ecosystem plays with upstream carriers and third-party scrubbing.
CHAPTERFeature Breakdown
Core Capabilities
-
Sub-second anomaly detection and classification
- Technical: Per-host time-series baselining with per-second PPS checks and feature extraction (protocol mix, SYN/ACK ratios, entropy signals). IOC matching accelerates attribution (e.g., Mirai-variant fingerprints).
- Use case: A game server spikes from 80k to 2.5M PPS of UDP; agent flags within 1 second, tags “UDP flood,” and moves to step-1 FlowSpec block.
-
Automated network enforcement (BGP FlowSpec/RTBH + scrubbing)
- Technical: On alert, Flowtriq programmatically installs FlowSpec on edge routers, triggers RTBH when volumetrics exceed local capacity, or signals cloud scrubbing providers. Policies can chain: FlowSpec (60s) → RTBH source /32 (burst) → Magic Transit diversion (sustained).
- Use case: ISP with 200 nodes: initial FlowSpec cuts 90% of junk; sustained L3/L4 volume exceeds links, so traffic diverts to provider scrubbing automatically.
-
Forensic-grade capture and runbooks
- Technical: Auto-initiated full PCAP per incident, plus automated incident response runbooks that chain mitigations, notifications, and status page updates. Immutable audit logs ensure tamper-evident traceability.
- Use case: SaaS edge node hit by mixed SYN + HTTP flood; PCAP supports post-mortem, while a runbook pages on-call via PagerDuty, posts to Slack, and updates a customer-facing status page.
Integration Ecosystem
Flowtriq exposes webhooks for custom pipelines and supports multi-channel alerting (Discord, Slack, PagerDuty, OpsGenie, SMS, email) that fire within one second. Upstream integrations include Cloudflare Magic Transit, OVH VAC, and Hetzner for scrubbing. BGP FlowSpec/RTBH tie into your routing stack; incident runbooks can call internal APIs for WAF rules or autoscaling. The platform’s Threat Intel and IOC correlation enrich detections, while Attack Profiles let teams codify recurring signatures and responses—useful for MSPs standardizing defenses across tenants in Marketplace Tech contexts.
Security & Compliance
Data handling is pragmatic: packet inspection happens on-host; only telemetry, alerts, and PCAPs (on incident) leave the node. Enterprise options include custom IOC libraries and 365-day PCAP retention. Immutable audit logs bolster evidentiary needs. Certifications aren’t listed; security teams should assess data residency and retention policies during procurement. Principle of least privilege applies—restrict BGP change scopes and segregate credentials for scrubbing provider APIs.
CHAPTERPerformance Considerations
The agent’s packet-level analysis yields sub-second MTTD/MTTR, reducing collateral damage for bursty attacks. Overhead is workload- and PPS-dependent; on high-throughput hosts, isolate ftagent CPU/memory via cgroups and tune NIC offloads where needed. Since volumetric absorptions ultimately depend on upstream capacity, FlowSpec/RTBH and scrubbing pivots are essential for link-saturating events. Reliability benefits from per-node autonomy—detections continue even if the control plane is temporarily unreachable.
CHAPTERHow It Compares Technically
- Cloudflare Magic Transit: carrier/edge scrubbing with global anycast and BGP-based diversion; excels at volumetrics but is perimeter-first. Deep dive: https://developers.cloudflare.com/magic-transit/
- Akamai Prolexic: managed scrubbing with massive capacity; strongest at sustained, multi-vector campaigns. Deep dive: https://www.akamai.com/products/prolexic
- NETSCOUT Arbor (AED/TMS): appliance + carrier integrations; rich network telemetry and mitigation. Deep dive: https://www.netscout.com/product/arbor-ddos
- Radware DefensePro: inline appliance with behavioral and signature engines; low-latency inline mitigation. Deep dive: https://www.radware.com/products/defensepro/
- Corero SmartWall: always-on inline protection for ISPs/data centers. Deep dive: https://www.corero.com/products/
- FastNetMon: flow-based detection (sFlow/NetFlow/IPFIX) vs. host packet capture; strong NOC fit. Deep dive: https://fastnetmon.com/
Flowtriq’s differentiation: host-based packet inspection with automated BGP/RTBH/scrubbing orchestration—closer to the workload than flow collectors and lighter to adopt than inline appliances. It complements edge scrubbing rather than replacing it.
CHAPTERDeveloper Experience
Install-to-first-signal in under two minutes via the Python agent—no manual threshold tuning. The dashboard centralizes multi-node policy, runbooks, and status pages; alert integrations cover the standard SRE stack. Flowtriq’s published research (e.g., Mirai kill switch, CVE-2024-45163), the “State of DDoS 2026” report, free certifications, and tooling (FlowSpec builder, PCAP analyzer, iptables generator) signal a practitioner-centric ecosystem that accelerates onboarding and operational fluency.
CHAPTERTechnical Verdict
Flowtriq is a pragmatic Platform Tool for infrastructure teams seeking sub-second detection, automated network enforcement, and actionable forensics at a flat $9.99/node/month ($7.99 annual). Strengths: agent-based granularity, dynamic baselines, robust alerting, IOC correlation, and orchestration into BGP and major scrubbers—an effective Ecosystem Play. Limitations: Linux-only agent, dependency on upstream capacity for large volumetrics, and the need for BGP/peering control to exploit FlowSpec/RTBH. Ideal for hosting providers, ISPs/MSPs, game servers, and SaaS edges that want rapid time-to-value with low run costs and a clear path to integrate with existing scrubbing strategies amid evolving Platform Trends.
EXPLORE FLOWTRIQ
VISIT WEBSITE →